
Closing the AI agent identity governance gap
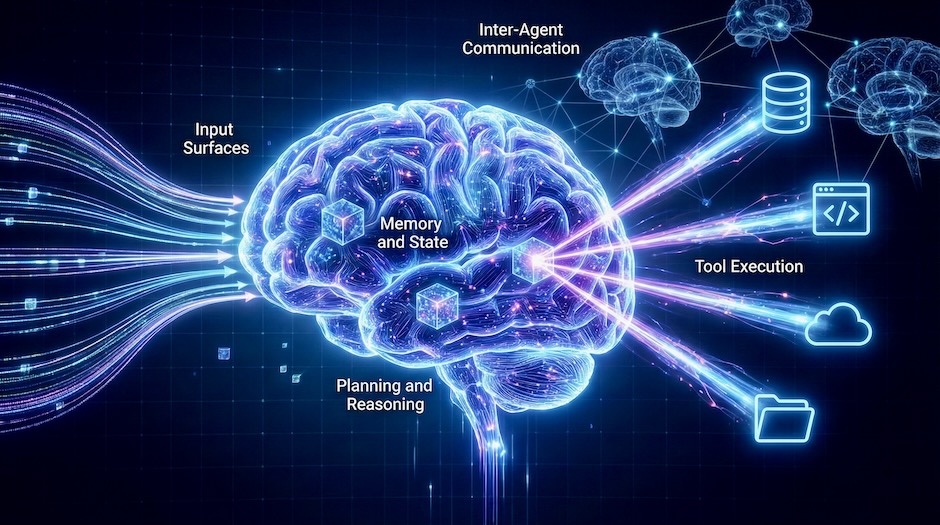
AI agents are a rapidly growing class of non-human identities, yet most IAM programs still treat them like ordinary service accounts.

AI agents are a rapidly growing class of non-human identities, yet most IAM programs still treat them like ordinary service accounts.
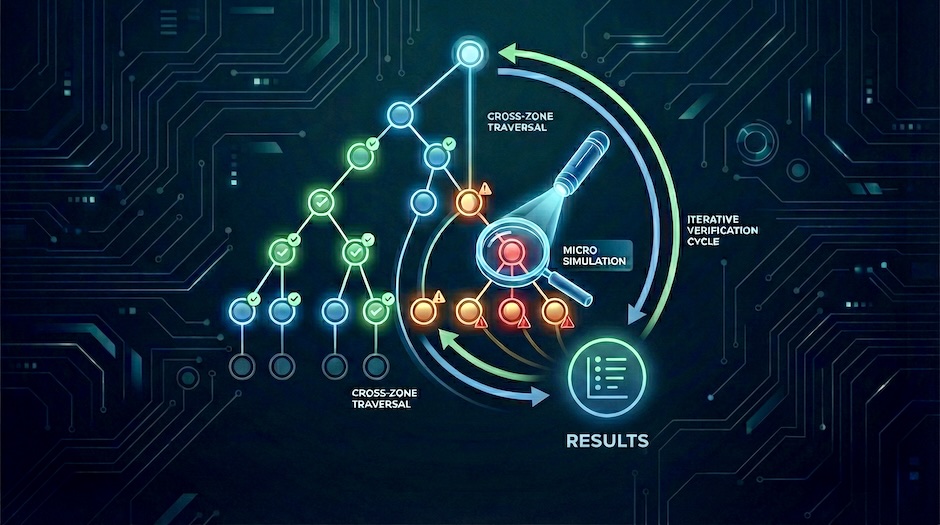
Move agentic AI threat models from assumptions to tested control assertions using attack-tree-driven micro simulations.

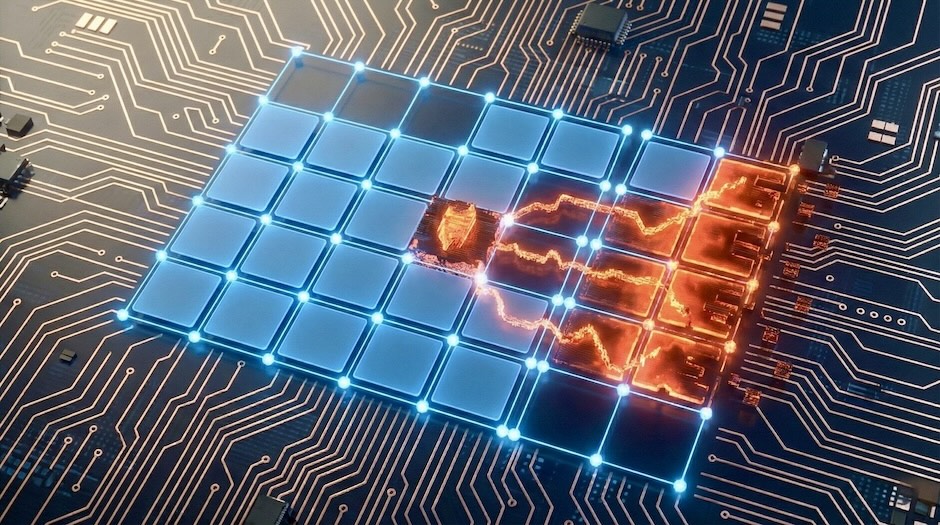
How attackers bypass text-based guardrails by embedding malicious instructions in images and audio, and the layered defenses required to counter them.
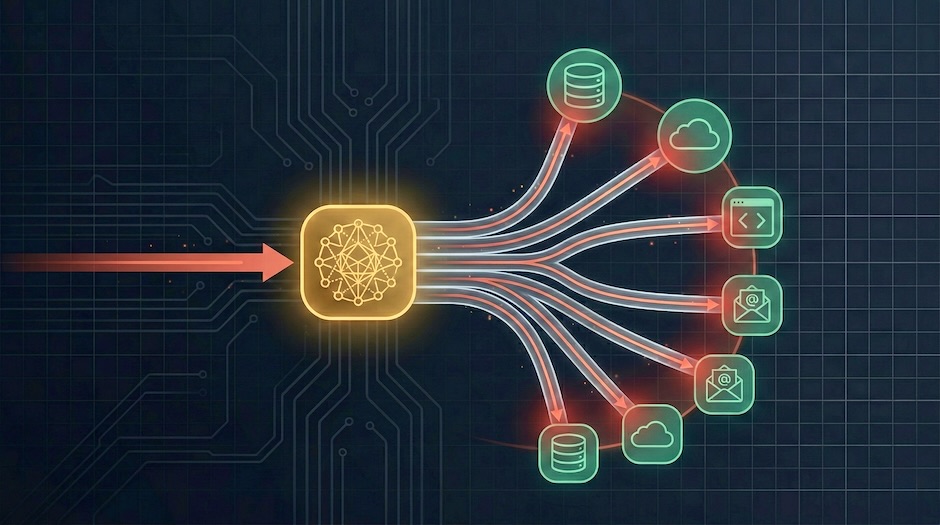
AI agents create a third class of lateral movement, bridging previously isolated systems through natural language, tool access, and execution autonomy.
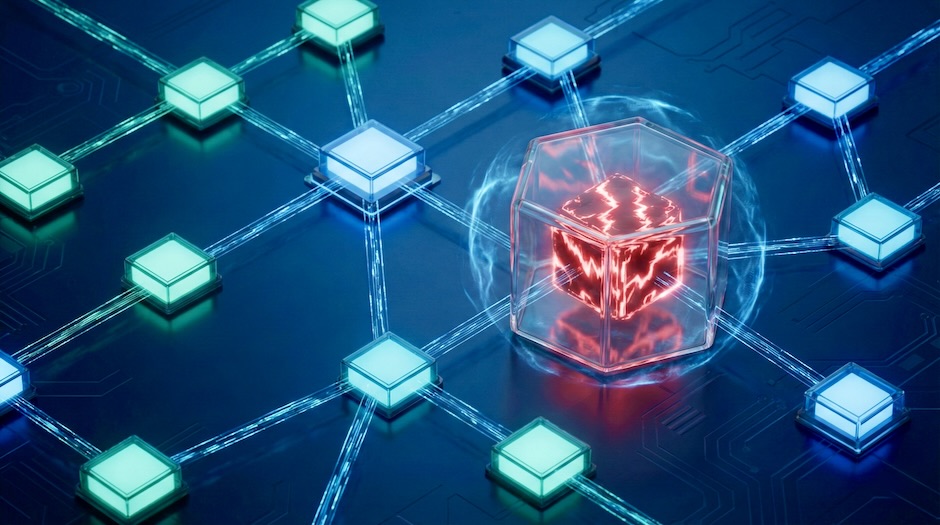
How attackers plant instructions targeting agentic AI systems today that execute weeks later, and the defense architecture that stops them.

Why your sanitized user queries don’t protect you when the threat enters through your knowledge base.
Why the Model Context Protocol needs a new security mental model, and how to build it.
A scenario-driven workflow for tracing attack paths in agentic AI systems using a five-zone navigation lens, attack trees, and OWASP’s threat taxonomy and playbooks.

How the shift from single-model LLM integrations to agentic AI systems amplifies prompt injection into a multi-step attack chain.