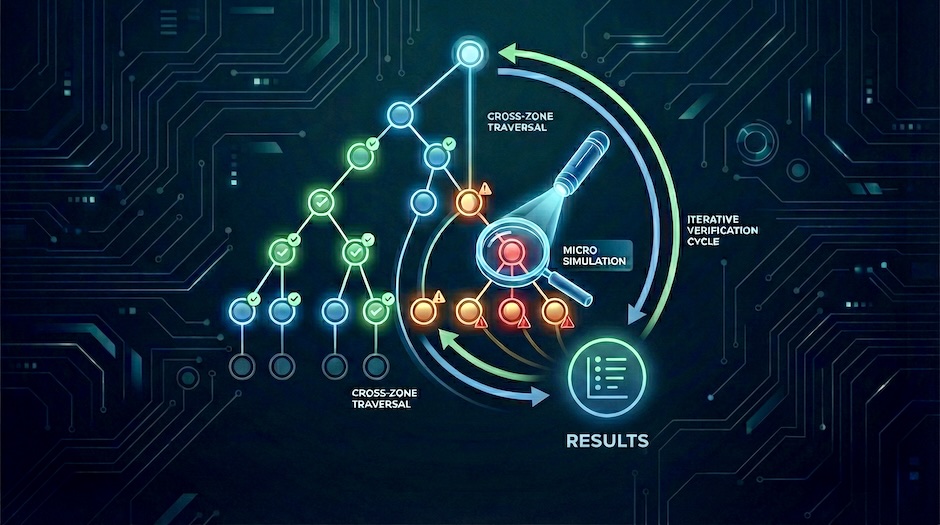
Verifying agentic AI controls with attack tree micro simulations
Move agentic AI threat models from assumptions to tested control assertions using attack-tree-driven micro simulations.
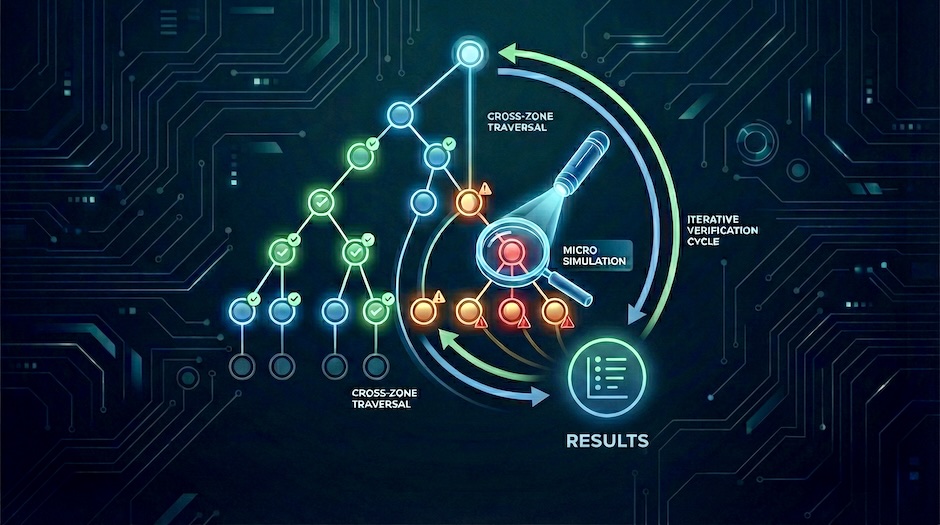
Move agentic AI threat models from assumptions to tested control assertions using attack-tree-driven micro simulations.
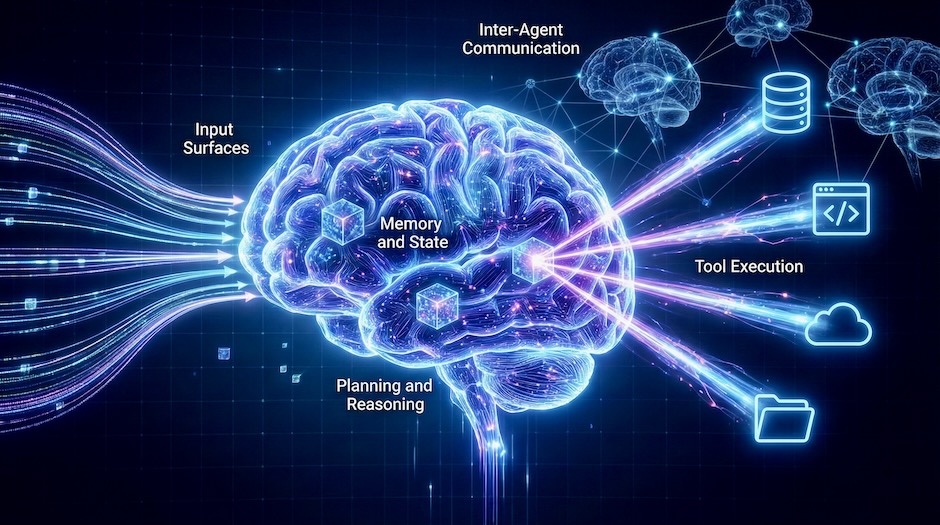
A scenario-driven workflow for tracing attack paths in agentic AI systems using a five-zone navigation lens, attack trees, and OWASP’s threat taxonomy and playbooks.

I was interviewed about improving cyber resilience through Micro Attack Simulations.