Verifying agentic AI controls with attack tree micro simulations
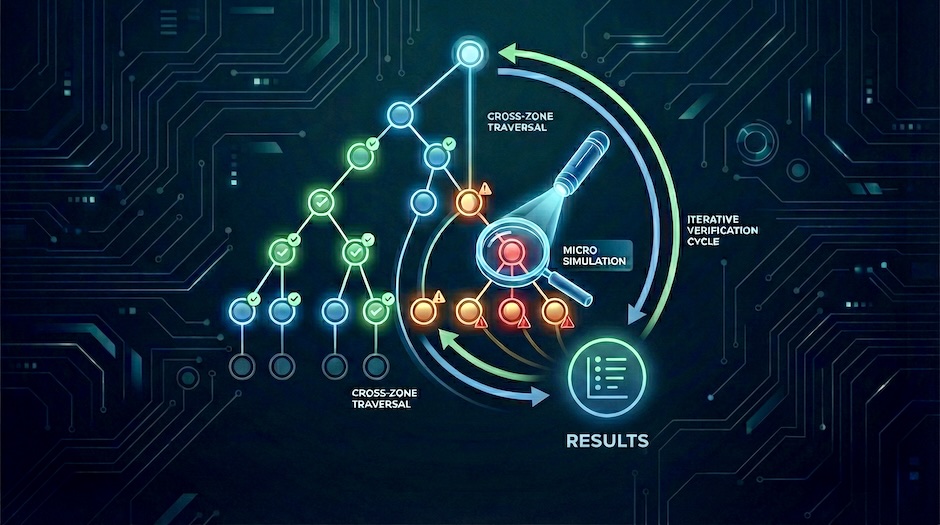
Move agentic AI threat models from assumptions to tested control assertions using attack-tree-driven micro simulations.
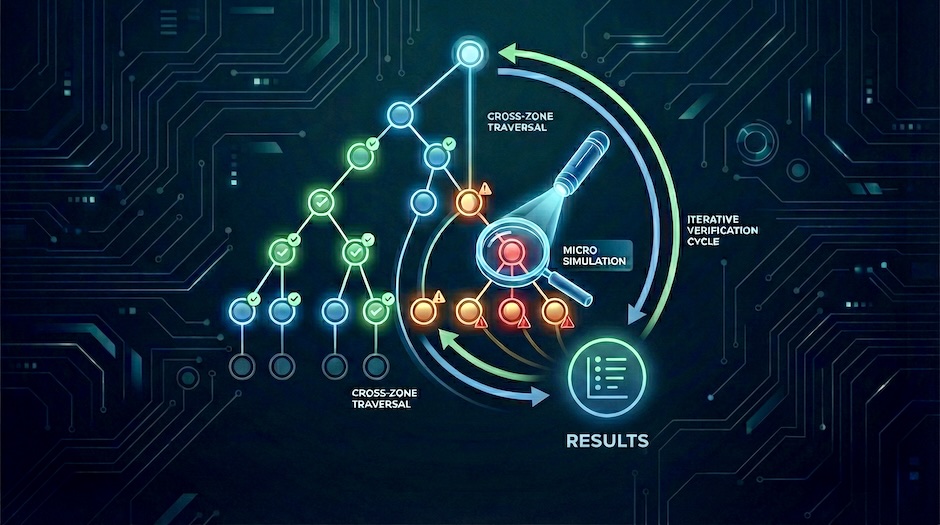
Move agentic AI threat models from assumptions to tested control assertions using attack-tree-driven micro simulations.

I was interviewed about improving cyber resilience through Micro Attack Simulations.

Details about the vulnerability class Untrusted Deserialization.

Writeup of my Same-Origin Policy Bypass in Chrome with SVG (CVE-2014-3160).

Generic Detection of XML External Entity (XXE) Vulnerabilities.

Details about the vulnerability class I identified in the HTML5 WebSocket specification (RFC 6455).